HoneyMex Lab
Deception & Honeypots, Network Security, Threat Intel, Cybersecurity research and more.
Open Research Community - Honeynet Mexico Lab
About the project
HoneyMex Lab is an independent, open research cybersecurity group organized by volunteers with diverse backgrounds, including DFIR, Threat Hunting, System Administration, Threat Intelligence, and Cyber Deception/Honeypots.
HoneyMex Lab is a spin-off initiative of Mizton Labs to operate the Honeynet Mexico Chapter of The Honeynet Project and continue developing new projects inspired by the previous work of former UNAM-Chapter. The vision of HoneyMex Lab is to become a reference in the LATAM region.
Our members and collaborators come from both industry and academia. The team's roots trace back to projects developed or inspired by work within the former UNAM-CERT and The Honeynet Project as UNAM Chapter (Mirror archive).
Our Main Focus Areas Include:
- - Deception and Honeypot Research & Development
- - Threat Detection Engineering
- - Network Security
- - Network Forensics
- - Malware Analysis
- - Yes.. AI and CyberSecurity (LLM-based deception/honeypot, LLM Security, etc)
Our Blog and News
Check out our latest activity
Technical articles, security news, events, tutoriasl, and more.

The TeamPCP group (UNC6780) compromised a GitHub employee's device through a trojanized VS Code extension, exfiltrating approximately 3,800 internal repositories from the platform in May 2026.
obeedt, OscarRV, LuisZavMen
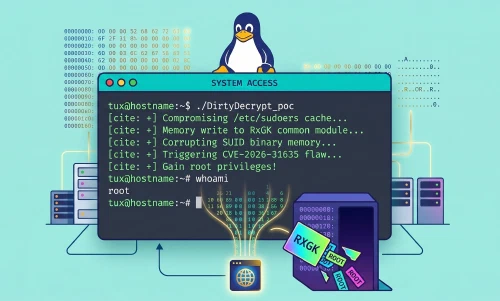
An inverted validation flaw in the rxgk module allows local attackers to bypass the Copy-On-Write (COW) mechanism and corrupt the page cache to gain root access.
obeedt, OscarRV, LuisZavMen
A memory handling flaw during data copy operations allows any unprivileged user to gain full control of a Linux system.
obeedt, OscarRV, LuisZavMen